Phishing: An Overlooked Threat to Business and Data
Data is the lifeblood of an organization and businesses that fail to embrace this fundamental concept risk losing future business opportunities or the company itself. The value of business and consumer data hasn’t been lost on cybercriminals, which is why phishing attacks and other data security threats have been more rampant through the years. As data technology becomes more advanced, reliance on data becomes a more significant opportunity for exploitation as even the most advanced data systems have their vulnerabilities. Businesses collect and process large amounts of data from several sources, making the protection of this data one of their main challenges.
The Threat to Business and Data
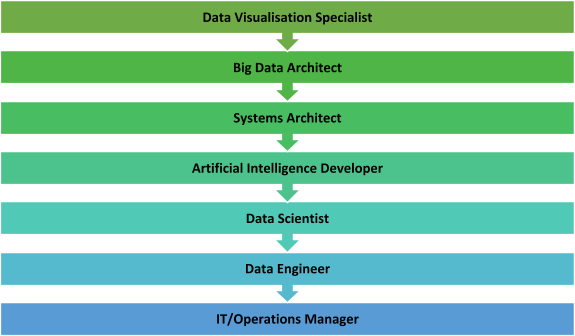
Today’s businesses demand a lot from the data they collect, and as such, also look for solutions that will help transform data into more tangible bits and pieces that will help promote business success. The role of AI in cybersecurity has been gaining mainstream attention because it helps automate the detection of security threats and other malicious activities within a company’s systems.
Looking to more advanced solutions for cybersecurity is a prudent approach, and is highly recommended, especially for businesses that handle large amounts of data daily. Cybersecurity threats are no laughing matter, and they’re becoming more advanced and difficult to identify and address. The end goal remains the same, however—to gain unauthorized access to data and use it to harm a business or for personal gain. The threats come in many forms, including DDoS attacks, malware, and phishing attacks.
Cybersecurity threats are serious not only due to the potential loss of data but also because a data breach can cause irreparable harm to a business. Give cybercriminals access to sensitive data and there’s no telling what damage they’ll cause. Even a simple phishing scam can lead to a full-blown data breach, and these breaches rely on users making mistakes.
Recognizing Phishing Scams
Before businesses can combat scams, they must train their employees on the detection and proper ways of addressing or preventing them altogether. Below are the most common types of phishing attacks done against businesses.
Phishing Emails
Phishing emails are common in a business email inbox—typically categorized together with spam emails. The difference is that they are not simply unsolicited marketing messages; they are designed to trick you into opening a malicious attachment or clicking on a link to a fraudulent website. Scammers often use an email address that resembles a legitimate business email address to confuse users into thinking that the email came from someone within the organization or a trusted partner or a third party.
Company Impersonation
This method is a type of phishing scam in which scammers try to impersonate your brand. This is often done via “domain spoofing” or using a fake but similar website or email domain designed to confuse the recipients of the email. It can be difficult to detect as a source of a data breach because it’s often unreported. Victims of these scams often aren’t aware that they’ve been duped until it’s too late.
Phone Phishing/Voice Phishing
This is similar to company impersonation but uses a different medium—Voice over Internet Protocol (VoIP). Most scammers who use this method go so far as to imitate the tone of voice and spiels of the brands they’re trying to impersonate. This is usually done in conjunction with other phishing scams to increase the chances of success.
Spear phishing
This is similar to phishing emails but with a more targeted approach. It involves more effort on the scammers’ part because it entails getting key information about a target. Using this method, the scammers send an email containing the name of a company officer and other personalizations to make the recipient believe that the email is legitimate. Unsuspecting users will be duped into sending money, pertinent information, or making payments to a fake vendor or partner. It’s a sophisticated scam that can often trick even tech-savvy individuals, depending on how skillfully the fake email message is crafted.
Email Account Takeover
It’s one thing to have scammers send fake emails and try to make them look legitimate, but it’s another when they get access to a legitimate email account and use it to get money from unsuspecting users, gain access to sensitive information, or cause harm to a business. It’s typically done as part of a cross-account takeover, in which a scammer gains access to a user’s email account, changes the password, and proceeds to make fund transfers from the compromised user’s bank and other financial accounts.
Why Cyberattackers Resort to Phishing Scams
Phishing scams are one of the most common cyberattacks that threaten the security of the company and personal data, with spear phishing being one of the main infection vectors. It’s a common scam because phishing is as easy; anyone can execute a phishing attack and be relatively successful with little to no investment. The flexibility of a phishing scam also makes it an infection vector of choice. With it, a scammer can steal sensitive data and gain access to user accounts.
The simplicity-to-value ratio is also a tempting draw of phishing. Despite how simple its execution is, it can help cybercriminals get their hands on large sums of money. $17,700 is lost every minute because of a phishing scam.
Lastly, users aren’t good at putting a stop to scams—even large companies face the threat of phishing today. Because of how sophisticated these phishing emails have become and the large number of emails people have to go through each day, it can distinguish a fake email from a real one.
Fighting the Good Fight
Despite the evolving threats to data security, there are still ways you can fight them. Just like cybercriminals always find vulnerabilities to exploit, you can always find ways to mitigate or even counteract these measures. The key is in keeping an open eye and mind and keeping abreast of the available solutions that can help you keep your data and business secure. Protecting your digital assets often requires “digital measures.” It won’t hurt to let digital tools help you, but you and your organization should be at the heart of your data security. Educate yourself and your employees so your security isn’t only as good as the tool you choose to use.













 Ross Perez is the Senior Director, Marketing EMEA at
Ross Perez is the Senior Director, Marketing EMEA at 